As social networks grow, so do issues regarding who can view the content. Researchers from England teamed up to conceptualize and design the Personal Agent for Access Control in Social Media (nicknamed “PACMAN”), a soon-to-be smartphone application. This novel approach employs machine learning algorithms to automatically make social media access control decisions by combining information about both social relationships and content.
“To the best of my knowledge, none of the mainstream social media sites are providing automatic access control assistance for their users,” said Gaurav Misra, researcher at Lancaster University. “They provide varying degrees of assistance in contextualizing relationships between the user and their contacts, but the burden of making access control decisions lies on the user.”
Once developed, PACMAN will examine a user’s social network to provide access control recommendations via “allow” and “deny” options. This can ease a user’s worries of sharing sensitive content with certain people in their network.
While working with machine learning algorithms, PACMAN evaluates relationship type (by leveraging the structure of the user’s social network), relationship strength (shared contacts or mutual friends), and the content a user is sharing before delivering a recommendation (depicted in Figure 1 below). Since users have various types and strengths of relationships in their network, it is critical to analyze each connection and the content they would receive individually.
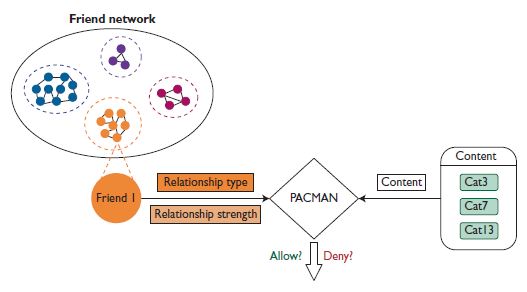
Figure 1: Components and Inputs of PACMAN’s access control system
For example, if a user posts on a political issue, and they previously restricted their uncle from viewing that category, PACMAN would make it so all the user’s family members would not be able to view the post.
Currently a proof-of-concept, researchers evaluated PACMAN’s success through an exercise that required social media users to make access control decisions while sharing photos. This was comprised of five randomly selected images via the application software and five user-selected images. The user was asked to categorize each photo and select who could/could not view the images from that category. After compiling this information, they found that PACMAN made accurate decisions 91.8 percent of the time across 26 initial users.
Once commercialized, however, PACMAN will automatically pull in information about the type and strength of a relationship to immediately make access control decisions. Users are given the option to manually adjust these decisions, and based on that, the accuracy of the recommendations will improve with time as it continues to “learn” a user’s preferences.
As for the actual use of PACMAN, there’s no guarantee it would have a high adoption rate amongst users. Still, Misra believes it’s a step in the right direction.
“The essence of PACMAN is that it doesn’t require a lot of effort from users,” said Misra. “Therefore, using PACMAN would not impede their social media activity. PACMAN doesn’t require any personal information, so the privacy concerns with using PACMAN are minimal. There’s no “one-size-fits-all” solution and therefore personalization is a major focus for PACMAN going forward. For these reasons, I do believe that PACMAN will be an improvement on state-of-art solutions available to social media users.”
Additionally, the researchers are looking to rework this application for social media channels other than Facebook, as well as commercialize and deploy the application for widespread use.
According to the researchers, their findings show that on Facebook alone there are more than 1 billion users sharing over 300 petabytes of personal information daily. Users build networks of family members, friends, colleagues and acquaintances, but don’t have the ability to control the delivery of their message like they would in person—PACMAN works to seamlessly solve this issue.
For more information on access control, visit the IEEE Xplore Digital Library.