Securing data on wearables is a challenge that has stumped many a device maker. But a recent first-of-its-kind study shows that combining voice and touch recognition may be the key to preventing hackers from gaining access to personal data.
Researchers from the College of William and Mary say they are the first to combine behavioral biometrics from different dimensions, such as touch gestures, with voice commands for use with wearable glasses. Their study on a novel continuous authentication system for increased privacy protection could be a breakthrough that makes it virtually impossible to replicate or steal information that can be used to hack into the smart device.
Currently, most major wearable glasses use on-head detection privacy, which automatically locks the glasses when removed. This can be unreliable as glasses sometimes fail to lock when a user takes off his or her device, allowing an imposter to act as the user if obtained.
Even when on-head detection is properly working and requires a user to enter one-time authentication credentials, there is potential for hacking. Imposters can easily get past one-time authentication systems with smudge attacks (identifying the oil streak that a user’s finger leaves behind when unlocking) or by simply peeking as the credentials are entered. To combat these problems, the researchers created GlassGuard – a continuous and non-invasive user authentication system that can identify an owner from an imposter.
Though touch biometrics and voice commands are both common ways to secure smart devices, incorporating both kinds of security measures creates a stronger protection system to combat potential hacking scenarios.
“A continuous authentication system based only on touch biometrics can be easily circumvented by using voice commands,” said Ge Peng, researcher at the College of William and Mary. “Similarly, a system purely based on voice authentication does not always work, as voice commands are not available all the time. A user may be in a situation when speaking is not appropriate.”
With six types of touch interactions (including single-tap, swipe forward, swipe backward, swipe down, two-finger swipe forward, two-finger swipe backward) along with vocal recognition, the continuous authentication system uses classifiers to identify the wearer and grant access. This machine learning process can be seen in Figure 1 below.
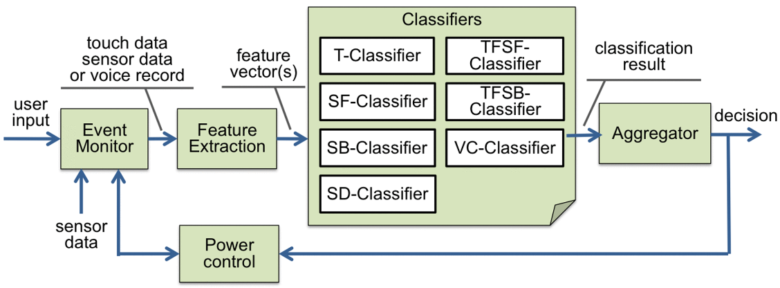
Figure 1: GlassGuard continuous authentication process
Once the seven classifiers have been implemented, an aggregator is used to synthesize the biometric information to come to a conclusion on whether the current wearer is the owner.
The system classifies each touch or voice interaction as either positive (meaning the event most likely came from the device owner), or negative (where the event most likely came from an imposter). Combining multiple classification results from a series of interactions, the aggregator calculates a likelihood ratio, which indicates how likely the current user is the actual owner, and makes the final decision.
When the likelihood ratio reaches an upper threshold, the system predicts the user as the owner. When it drops below a lower threshold, the system predicts the user as an imposter. If the ratio falls between the two thresholds, the system is unable to make an accurate decision and will postpone making that decision until it can analyze more user events. Typically, it takes four to five user events for the system to make the decision.
In an initial study of 32 users, results showed that GlassGuard had a 99 percent accurate detection rate, and a 0.5 percent false alarm rate, after an average of only 3.5 user events.
The next step for the researchers is to measure the power consumption of GlassGuard’s continuous authentication system and analyze its performance. The performance will measure long term, routine use of wearable glasses by a larger sample size.
With further research and new ways of enabling smart devices to better identify potential hacking opportunities, one-time authentication systems could become a thing of the past. And by combining various biometrics, this system model may be the key to the future of data privacy protection.
Learn more about wearable glasses in IEEE Xplore.





